Welcome to my technical blog!
Here, you’ll find useful insights and knowledge to help you stay ahead in the industry.
Thanks for stopping by, and I hope you enjoy what you read.
Find about me more ⬇️

[Golang] Writing Elegant Go Code Without Overengineering It
If you’ve been working with Go for a while and find your code resembling a plate of spaghetti, rest assured you’re not alone. This is a common challenge many developers encounter over time. The issue often isn’t a lack of design patterns or frameworks, but rather the misuse of abstractions at the wrong moments. Writing elegant Go code is about increasing readability, not demonstrating cleverness. This post outlines essential principles to transform complicated and tangled Go code into a cleaner and more maintainable form—without drifting into complex “enterprise abstraction soups.” ...
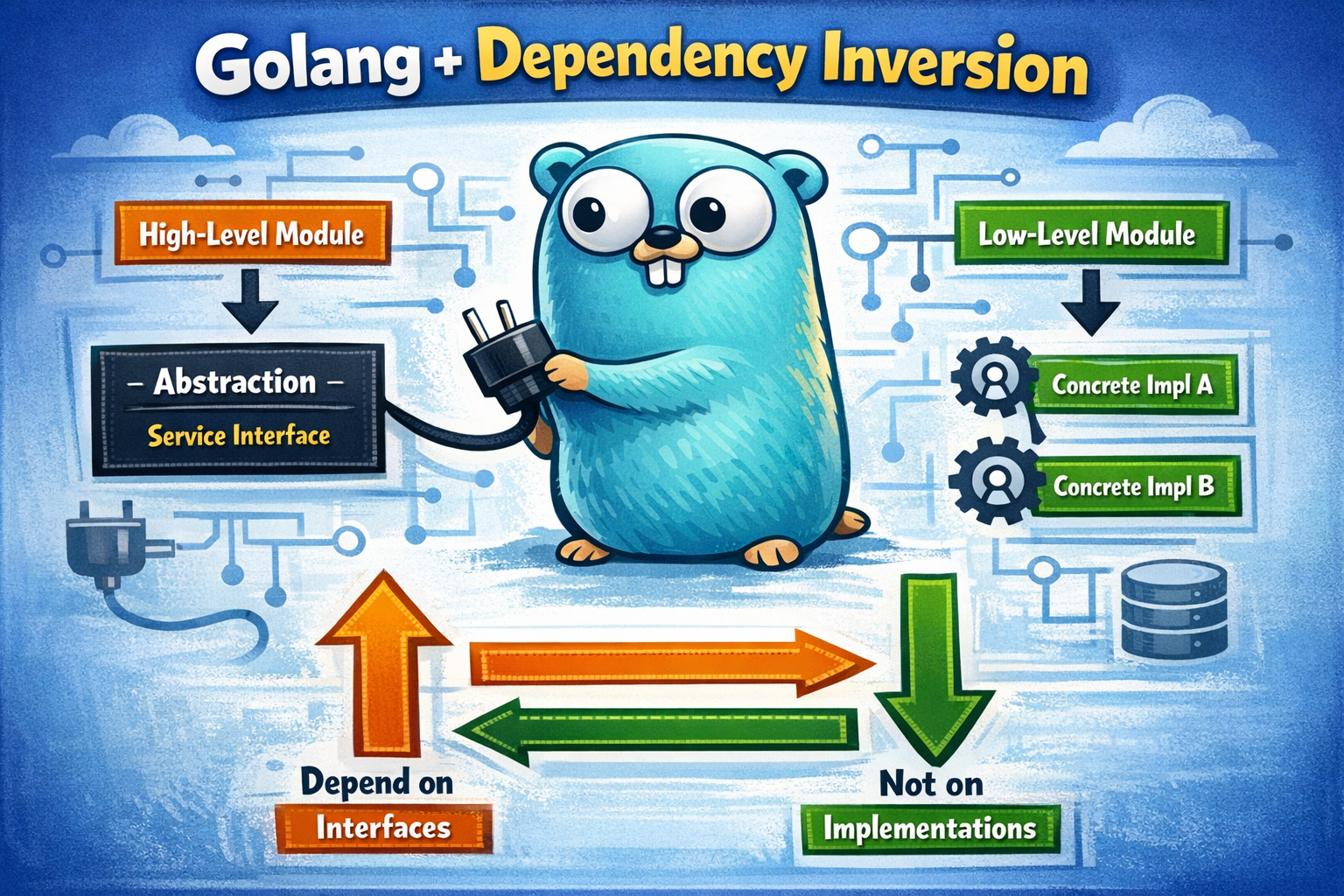
[Golang] Mastering Dependency Inversion: Keep Your Go Code Clean
Dependency inversion is a fundamental principle in software design that enhances code cleanliness, maintainability, and extensibility. While not exclusive to Go, the way it manifests in this language is particularly accessible and effective. At its heart, dependency inversion asserts that high-level components should not rely directly on low-level modules. Instead, both should depend on abstractions, fostering a more adaptable architecture. In practical Go development, this means crafting your business logic to interface with small abstractions that express what functionality is needed rather than focusing on how that functionality is implemented. This post dives into how to leverage this principle in Go, highlighting potential pitfalls and offering concrete examples to demonstrate correct implementation. ...

[Docker/Traefik] A Production-Ready Traefik Setup with Docker Compose
Running multiple services on a single virtual machine (VM) can quickly become a logistical challenge, particularly when it comes to managing access and ensuring security. A reverse proxy, therefore, becomes a central piece of infrastructure. Traefik stands out among the options, offering native Docker integration, automatic HTTPS using Let’s Encrypt, dynamic routing via labels, and minimal manual configuration. But while Traefik boasts many advantages, achieving a clean, production-ready setup requires more than a simple “it works” configuration. This article will walk through structuring a robust Traefik setup on a VM, highlight key configuration choices, and delve into a subtle trap involving basic authentication and Docker Compose that could easily trip you up. ...

[Golang] Understanding TCP: Debunking Misconceptions with Practical Examples
TCP might seem straightforward, especially when using Go. You set up a net.Conn, call Write to send data, Read to receive it, and everything just seems to work. It’s straightforward, minimal, and very Go-like. However, this simplicity can lead to misunderstandings because the details beneath the surface are easy to overlook. This blog post aims to demystify the real workings of TCP using practical examples, tackling common myths, all within the context of Go development. ...
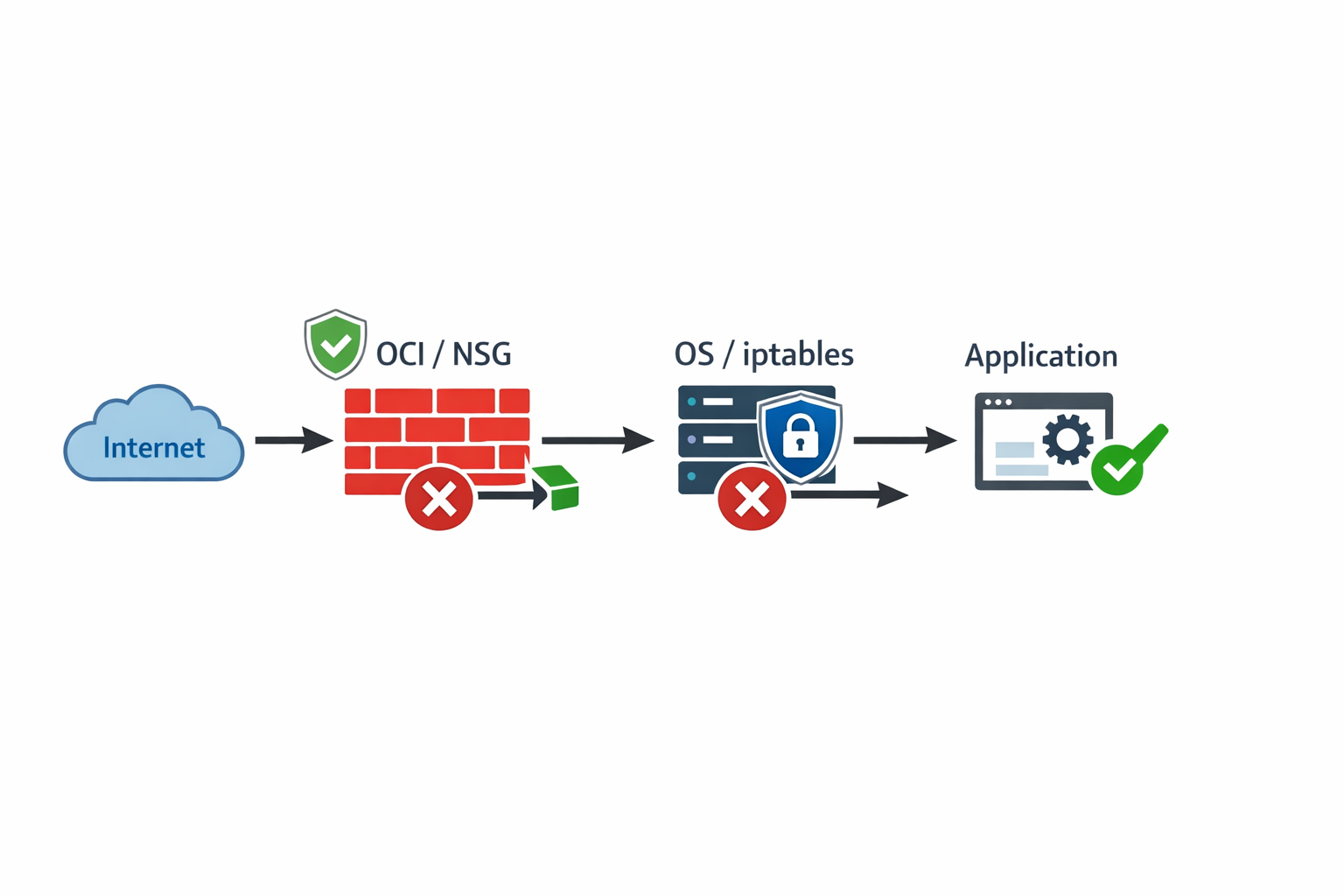
[OCI] How to Open a Port on an OCI Instance
Ever spent hours wrestling with an application that seems perfectly fine, only to hit a roadblock that feels completely invisible? Chances are, your application isn’t the problem. When deploying services on Oracle Cloud Infrastructure (OCI), connection failure is usually not a coding issue. It’s a network issue. Traffic, before it can reach your running code, must pass through a series of security checkpoints, each acting like a protective gate. The biggest mistake new users make is thinking that opening a port is a single action. In reality, OCI uses a layered security model, and if even one gate is closed, the connection fails. ...

[Golang] Avoid Using `defer mu.Unlock()` Inside Loops
In Go, using a mutex with defer might seem like an elegant and safe way to manage your code by ensuring resources are properly released. However, a common mistake lurks when this pattern is used inside loops. When working with mutexes, never do this: func broadcast(ctx context.Context, msgCh <-chan Message) { for { select { case msg := <-msgCh: s.mu.Lock() defer s.mu.Unlock() // ❌ Avoid this // Use the shared resource here case <-ctx.Done(): return } } } This seemingly harmless pattern can cause unexpected behavior and should be avoided. Let’s look into why this happens and how to handle it correctly. ...

[Kubernetes] Wait… Why Does Kubernetes Still Ask Me to Create a PersistentVolume? - The Storage Confusion Most Kubernetes Learners Hit
Introduction When I first learned Kubernetes storage, my mental model was very simple. In real clusters, we, as developers, usually have a StorageClass configured by Kubernetes administrators. So the workflow I saw everywhere looked like this: flowchart TB A["User creates a PersistentVolumeClaim (PVC)"] --> B["Kubernetes calls the CSI provisioner"] B --> C["Storage system creates a new disk"] C --> D["Kubernetes creates a PersistentVolume (PV) automatically"] D --> E["PVC binds to the PV"] In other words: PersistentVolumeClaim is enough. ...

[Golang] Stop Returning `(nil, nil)` in Go: A Small API Design Choice That Prevents Big Bugs
When designing Go APIs, you might think it’s harmless to return (nil, nil) when an object isn’t found. Many developers do this because it feels like “not found” shouldn’t be treated as an error. However, this approach often leads to one of the most frustrating runtime crashes in Go: panic: invalid memory address or nil pointer dereference In this post, we’ll cover: The problem — how (nil, nil) breeds fragile code Why this design creates real-world headaches Two solutions: Best practice (recommended): return a predefined error instead Alternative pattern: use an explicit existence flag An evolved, safer version of the code The goal isn’t just to fix mistakes, but to enhance API design to prevent misuse down the line. ...
[TLS] PEM vs CRT vs KEY Explained: Stop Guessing TLS Certificate Formats
If you have worked with TLS certificates, you may have encountered files with the extensions .pem, .crt, and .key. You might be wondering what they are, what differences they have, and how to use them effectively. The good news is that these formats aren’t as complicated as they seem once you understand the basics: PEM, CRT, and KEY are not different certificate types — they are different ways of packaging the same data. ...
Local HTTPS with Nginx in Minutes: A Practical Dev & Debug Setup (No Domain, No Public IP)
Setting up a local HTTPS environment is essential for developers wanting to test web applications under conditions that closely resemble production settings. This guide will help you establish a local Nginx reverse proxy using Docker Compose without the need for a domain or public IP, focusing specifically on Portainer as a sample application. Why You Want a Local Nginx Setup for Debugging When developing or debugging services like web dashboards or APIs, having an environment that closely mimics production is critical. A local Nginx reverse proxy enables you to: ...