Understanding Docker Credential Resolution: A Deep Dive for Developers
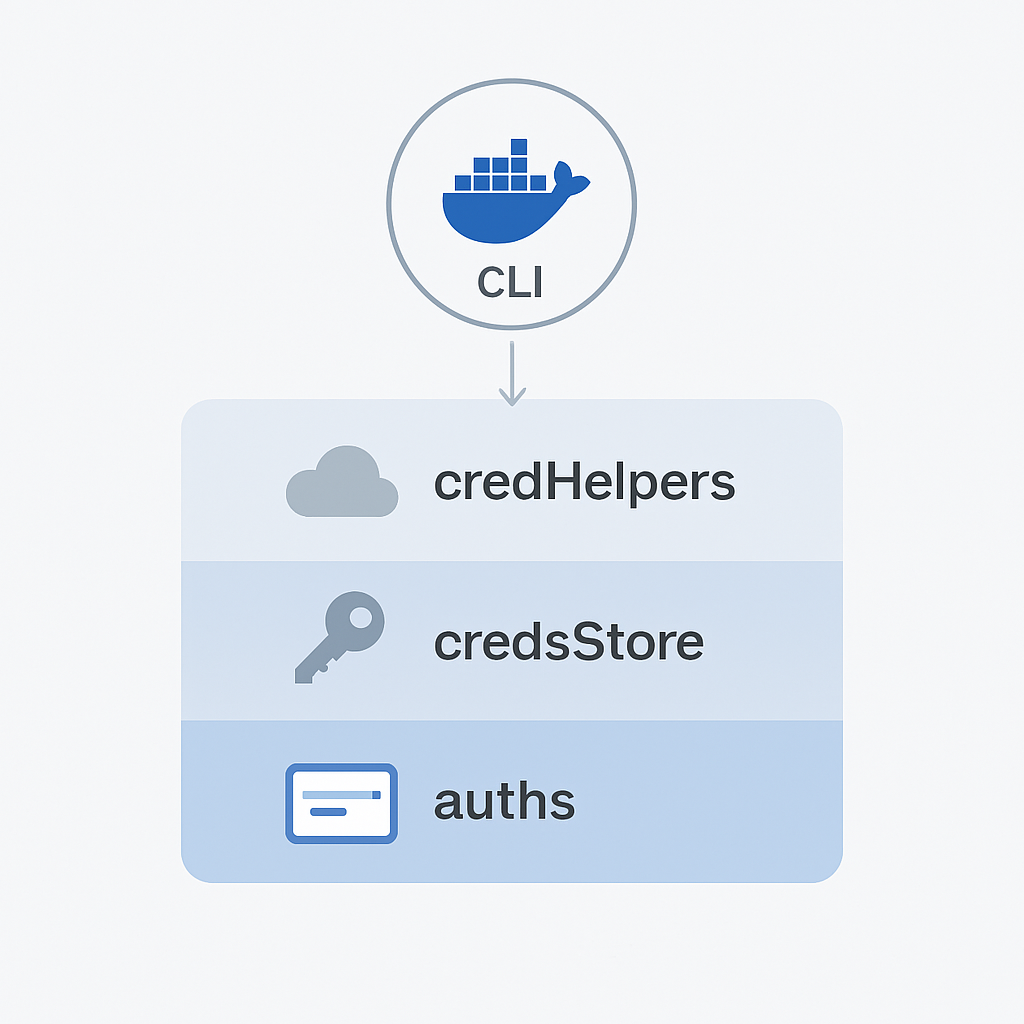
If you build your own container manage system when integrating docker client library, you may also encounter issues with credential resolution. If you system maintain the registry credential, it is easy to assume that authentication will “just work” once credentials are configured in your platform. But behind the scenes, Docker follows a specific and sometimes confusing logic for how it locates and uses credentials. This post explains that behavior in depth and highlights one of the most common causes of authentication issues developers face when using the Docker client as part of a backend or automation workflow. ...